CTCH 685 9040: Unit 2 Assignment: Secure Software and Software General Approaches
Unit 2 Assignment: Secure Software and Software General Approaches
Exercise 1: Identify the key fundamentals and principles of secure software development.
Perform the exercises and answer the following questions. Justify your responses and include citations from the learning resources as needed.
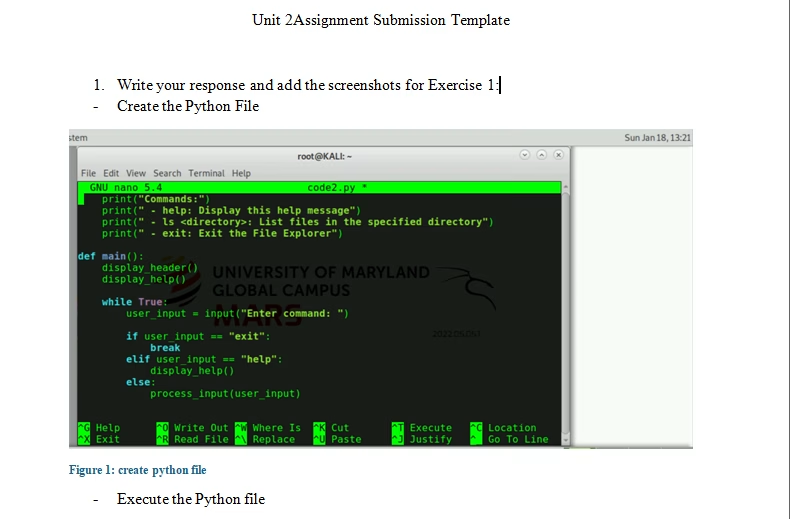
- Complete the Program Analysis for Software Vulnerability Discovery (Part 1) hands-on exercises.
- Place required screenshots into the Unit 2 Assignment Submission Template found in the submission instructions.
- Create a comprehensive overview of the secure software development life cycle (SSDLC) tailored to MedPeople’s biomedical technology context.
- Include phases such as requirements analysis, design, implementation, testing, deployment, and maintenance, emphasizing the importance of each phase in ensuring the security and integrity of the web application for patient data management.
Exercise 2: Analyze the primary characteristics that explain secure programming practices.
Answer the following questions. Justify your responses and include citations from the learning resources or the findings from the hands-on exercises as needed.
- Investigate and analyze the core principles of secure programming practices relevant to MedPeople’s web application development.
- Focus on characteristics like input validation, error handling, secure authentication, and authorization mechanisms, and discuss their significance in mitigating common security vulnerabilities such as buffer overflows, SQL injection, and cross-site scripting (XSS).
- Provide practical strategies for incorporating these characteristics into the software development process to enhance security.
Exercise 3: Describe common vulnerabilities found in various programming languages.
Answer the following questions. Justify your responses and include citations from the learning resources or the findings from the hands-on exercises as needed.
- Conduct a detailed examination of common vulnerabilities found in various programming languages, particularly those relevant to MedPeople’s web application development environment.
- Identify vulnerabilities such as injection flaws, broken authentication, sensitive data exposure, XML external entities (XXE), and others.
- Discuss the impact of these vulnerabilities on software security and provide mitigation strategies tailored to the specific programming languages used in MedPeople’s development stack.
Exercise 4: Summarize how libraries can introduce vulnerabilities into software and the general approaches to mitigate these vulnerabilities.
Answer the following questions. Justify your responses and include citations from the learning resources or the findings from the hands-on exercises as needed.
- Assess the security of the encryption library obtained from Find, Install and Publish Python Packages With the Python Package Index within the context of MedPeople’s web application development.
- Investigate potential vulnerabilities or weaknesses in the library and explore methods for testing its security, such as code review, penetration testing, or vulnerability scanning.
- Discuss the implications of using open-source libraries in software development projects, considering factors like reliability, community support, and vulnerability management.
- Describe how to design and implement session management capabilities that integrate authentication and access control modules to strengthen the security of MedPeople’s web application, aligning with industry best practices and standards.
Tutorial for Secure Software and Software General Approaches
$60.00
