CTCH 685 9040: Unit 6 Assignment: Space Layout Randomization (ASLR) in C Programs
Unit 6 Assignment: Space Layout Randomization (ASLR) in C Programs
Exercise 1: Engineer software components that not only fulfill their intended functions but also maintain a high standard of security integrity.
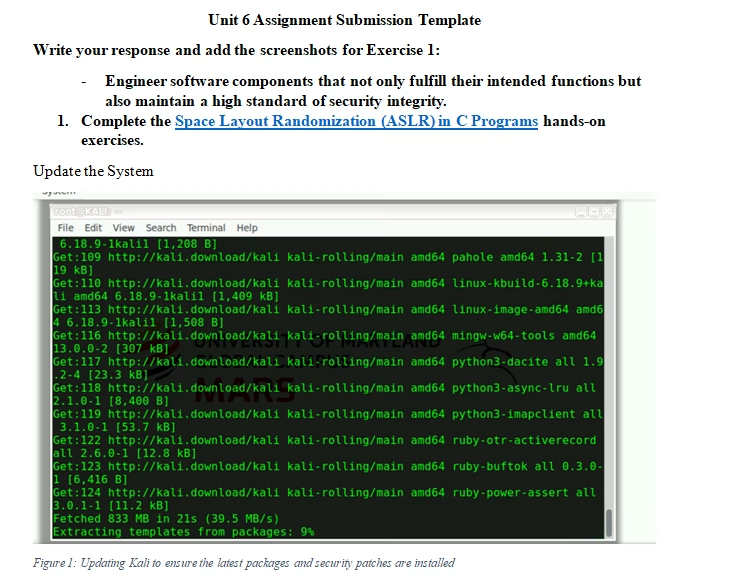
- Complete the Space Layout Randomization (ASLR) in C Programs hands-on exercises.
- What are the primary considerations in ensuring the security of software components while maintaining their functionality in a biomedical application like MedPeople’s?
- Focus on general software security practices, including secure coding guidelines and the integration of ASLR.
- What specific steps would you take to incorporate ASLR into the MedPeople web application to enhance its resilience against memory-based attacks?
Exercise 2: Simulate real-world exploitation scenarios to better understand and anticipate attacker strategies and behaviors.
- How would exploiting a stack-based buffer overflow in a medical application differ from exploiting it in a standard web application, and what additional precautions should be considered?
- Use examples from the hands-on exercises on stack-based buffer overflows and additional considerations for medical applications.
- Analyze how an attacker could exploit the ASLR mechanism in the MedPeople application. What strategies might they use, and what would be the impact?
- Describe the process of simulating a stack-based buffer overflow attack using the hands-on exercises. What tools and techniques did you use?
- How would you document and report your findings from a live exploitation exercise to ensure that the development team at MedPeople can effectively remediate identified vulnerabilities?
- Explain the best practices for documentation and reporting based on the results from the hands-on exercises.
Exercise 3: Critique the use of different programming techniques and library integrations in the context of security vulnerability prevention.
- Compare and contrast the use of static and dynamic code analysis tools in identifying vulnerabilities in the MedPeople web application. Which approach would be more effective and why?
- How do third-party libraries and frameworks contribute to the security or vulnerability of the MedPeople web application? Provide examples from the resources.
- Discuss using general best practices and examples related to library security.
- What criteria would you use to evaluate the security of a new library before integrating it into MedPeople’s web application?
Exercise 4: Execute defensive measures in software programming to counteract the vulnerabilities exposed during exploitation exercises.
- Develop a secure coding guideline tailored for the development team at MedPeople Corporation, incorporating specific defenses against buffer overflows and session hijacking.
- Use secure coding practices and insights from the hands-on exercises on buffer overflows.
- How would these measures specifically address the vulnerabilities exposed during the live exploitation exercises, considering the sensitive nature of the patient data handled by the web application?
- Detail how the measures would mitigate specific vulnerabilities identified during the exercises.
- Describe the process of implementing stack canaries and ASLR in the MedPeople web application. What challenges might you encounter, and how would you address them?
- Use the hands-on exercises and resources on ASLR and stack canaries.
- How would you use static code analysis to detect potential vulnerabilities in MedPeople’s application code? Provide a step-by-step approach based on the resources provided.
Tutorial for Space Layout Randomization (ASLR) in C Programs
$170.00
