CTCH 685 9040: Unit 1 Assignment Directions: Penetration Testing Part 1
Unit 1 Assignment Directions: Penetration Testing Part 1
Exercise 1: Penetration Testing
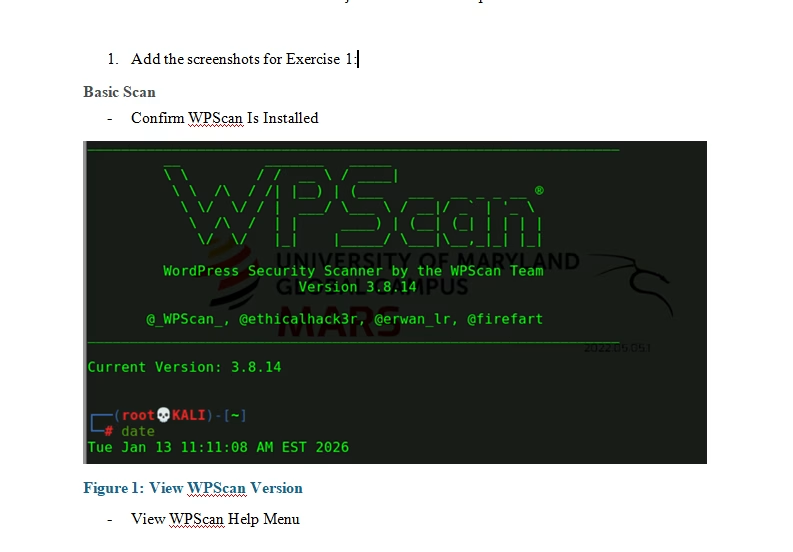
- Complete this hands-on exercise of Penetration Testing.
- Submit screenshots of all installations and commands in the Unit 1 Project Template
Exercise 2: Define the core fundamentals and principles of secure software development.
Answer the following questions. Justify your responses and include citations as needed.
- In any web application vulnerability assessment process, it is important to understand the steps by the browser to resolve any URL address. With the help of an illustrated diagram, demonstrate the steps your host takes to resolve your URL address.
- Explain at least five (5) different vulnerabilities or threats that can be found in a web application.
- As a CISO, the expectation is to have a security system that correctly identifies an attempted intrusion, penetration, or attack. Explain the differences between true, false positive, and false negative in a system event.
- What are the steps in resolving any of these system events (false positive or false negative)?
Exercise 3: List the characteristics that make programming secure, focusing on different programming paradigms.
Answer the following questions. Justify your responses and include citations as needed.
- What are the different strategies for mitigating web application vulnerabilities and threats?
- Session management is crucial to software security, what are the methods for handling user session data for software security?
Exercise 4: Summarize the vulnerabilities common to various programming languages.
Answer the following questions. Justify your responses and include citations as needed.
- In web application development, asynchronous JavaScript and XML, commonly known as AJAX, are used. There have been several concerns regarding AJAX’s behavior in terms of software security. Explain in detail “Ajax in Action” to illustrate a series of AJAX events in web development. You should also provide a real-life example of AJAX and its implementation.
- What are the advantages and disadvantages of implementing AJAX technology in a web application?
Exercise 5: Describe the types of vulnerabilities often introduced through the use of libraries.
Answer the following questions. Justify your responses and include citations as needed.
- In software development, what are the vulnerabilities that may occur when AJAX action does not properly check for cross-site request forgery attacks, authorization, or the contents of the uploaded archive file?
- Explain the security considerations of AJAX in its implementation.
Tutorial for Penetration Testing Part 1
$55.00
