CTCH 685 9040: Unit 3 Assignment: Penetration Testing for Software Threats
Unit 3 Assignment: Penetration Testing for Software Threats
Exercise 1: Develop software components that fulfill functional requirements while avoiding common security vulnerabilities.
Perform the exercises and answer the following questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
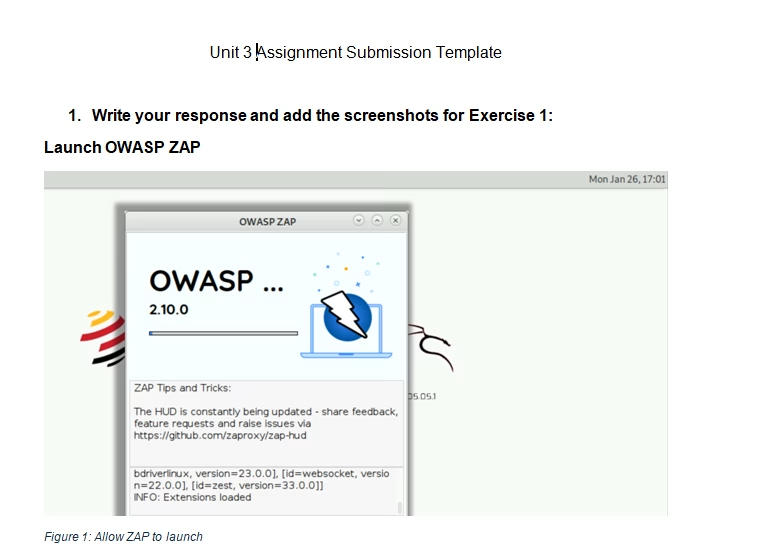
- Complete the Create a Web Penetration Tester.
- Place required screenshots into the Unit 3 Assignment Submission Template found in the submission instructions.
- How would you redesign the MedPeople Corporation’s web application’s architecture to ensure secure communication between various medical devices and the database, particularly focusing on preventing browser-powered desync attacks (BPDA)?
- Use the available resources to find the three most recent BPDA reports and identify the attacks most relevant to healthcare applications, summarizing their significance for MedPeople’s patient data security.
Exercise 2: Analyze specific cases of buffer overflows, SQL injection, and session hijacking to understand their mechanics and impacts.
Answer the following questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
- In the context of MedPeople’s web application, analyze how a server-side cache poisoning attack could affect patient data confidentiality and integrity.
- What would be the impact level of such an attack on the application’s functionality, and how could this compromise patient safety?
Exercise 3: Evaluate the effectiveness of different mitigation strategies for vulnerabilities introduced by libraries.
Answer the following questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
- After completing the Hands-On Exercise to Create a Web Penetration Tester and reviewing the research paper on security testing of web applications using Burp Suite, identify how the methodologies discussed can be applied to the MedPeople Corporation’s penetration testing efforts.
Exercise 4: Design a secure coding strategy to prevent vulnerabilities like buffer overflows, SQL injection, and session hijacking in software development.
Answer the following questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
- Develop a secure coding guideline tailored for the development team at MedPeople Corporation, incorporating specific defenses against SQL injection, buffer overflows, and session hijacking.
- How would these measures specifically address the vulnerabilities that could lead to browser-powered desync attacks and server-side cache poisoning, considering the sensitive nature of the patient data handled by the web application?
Tutorial for Penetration Testing for Software Threats
$45.00
