CTCH 685 9040: Unit 4 Assignment: Identify and Patch a Vulnerability
Unit 4 Assignment: Identify and Patch a Vulnerability
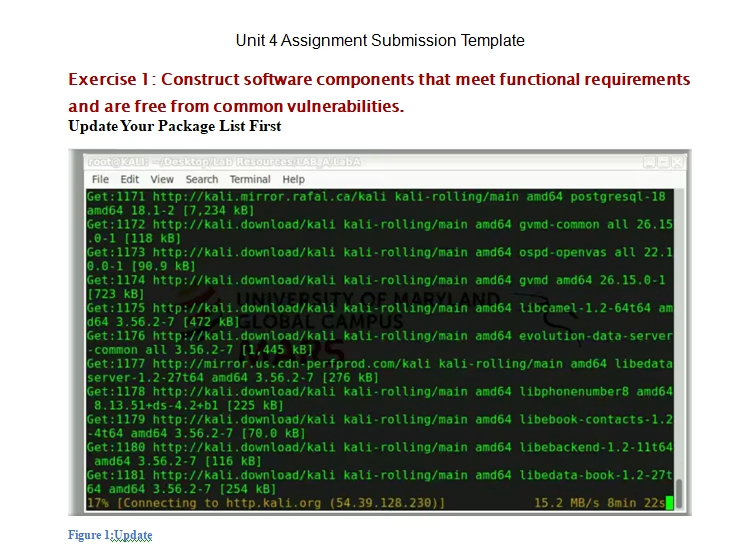
Exercise 1: Construct software components that meet functional requirements and are free from common vulnerabilities.
Perform the exercises and answer the following questions. Justify your responses and include citations as needed.
- Complete the Unit 4 Assignment Lab A Setup hands-on exercises.
- Identify and explain potential security risks or vulnerabilities detected in the code.
- Use the Secure Software Development Life Cycle (SSDLC) to describe the importance of analyzing code for security vulnerabilities without executing it.
- Complete the Unit 4 Assignment Lab A Mitigation hands-on exercises.
Exercise 2: Analyze the effectiveness of different programming techniques in avoiding vulnerabilities inherent in various programming languages.
Answer the following questions. Justify your responses and include citations as needed. Cite relevant CVE/NVD and other authoritative sources to justify your analysis.
- Explore the Common Vulnerabilities and Exposures (CVE) and National Vulnerability Database (NVD).
- Identify and analyze vulnerabilities related to “Typosquatting” that could affect MedPeople’s web application, focusing on understanding how these vulnerabilities can be exploited and their potential impact on the application’s security.
- Provide a detailed explanation of at least three typosquatting-related vulnerabilities, discussing their relevance to MedPeople’s biomedical technology context and the importance of mitigating these vulnerabilities to protect patient data.
Exercise 3: Evaluate the implementation of libraries in software projects, identifying potential vulnerabilities and proposing mitigation strategies.
Answer the following questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
- Describe the classification of fuzzers used in software testing, with a specific focus on mutation-based fuzzing techniques that generate new inputs from existing ones to uncover vulnerabilities.
- Explain how mutation fuzzers could be utilized to identify and mitigate potential vulnerabilities in MedPeople’s web application, enhancing the application’s resilience against attacks.
- Discuss the role of fuzz testing in the broader context of dynamic analysis and its importance in securing software applications, particularly those handling sensitive biomedical data.
Exercise 4: Apply advanced software testing and program analysis techniques as defensive measures against software vulnerabilities.
Answer the following questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
- Create a sample report on software testing and analysis techniques as defensive measures against software vulnerability for MedPeople.
- Analyze hypothetical scenarios where MedPeople’s web application could be vulnerable to attacks. Based on common vulnerabilities associated with web applications (e.g., SQL injection, XSS, CSRF), describe potential vulnerabilities in the application, possible exploitation methods, and the impact of such vulnerabilities on patient data and application integrity.
- Propose detailed mitigation strategies and security measures to address the hypothetical vulnerabilities identified in the previous task. Include recommendations for both immediate fixes and long-term security practices to be adopted by MedPeople.
Tutorial for Identify and Patch a Vulnerability
$43.00
