CTCH 685 9040: Unit 5 Assignment: Program Analysis for Software Vulnerability Discovery
Unit 5 Assignment: Program Analysis for Software Vulnerability Discovery
Exercise 1: Explain the foundational principles and concepts underlying secure software development.
Perform the following hands-on exercises and then answer the questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
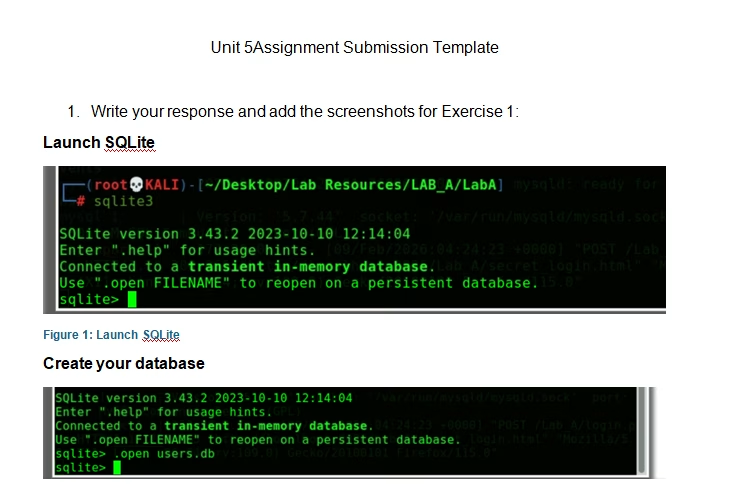
- Complete the Program Analysis for Software Vulnerability Discovery (Part 2) hands-on exercises.
- Place all screenshots in the Unit 5 template.
- Explain how the foundational principles of secure software development will be applied during the initial setup and configuration of MedPeople’s web application to preemptively address potential security vulnerabilities.
- Discuss how integrating SSDLC practices can enhance the security posture of the MedPeople’s web application from the early stages of development.
Exercise 2: Apply the distinct attributes that are essential for secure programming.
Answer the questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
- Identify which secure programming attributes are critical in securing the web application at MedPeople, particularly in terms of data handling and session management.
- Given the complexity of MedPeople’s web application, what secure programming practices would you implement to safeguard against SQL injection and cross-site scripting?
Exercise 3: Describe the specific vulnerabilities that are commonly found in various programming languages.
Answer the questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
- Can you identify any language-specific vulnerabilities within MedPeople’s web application that could potentially be exploited?
- How do these vulnerabilities affect the overall security of the web application, and what steps can be taken to mitigate these risks?
Exercise 4: Distinguish vulnerabilities that are often introduced by the usage of third-party libraries, along with basic mitigation techniques.
Answer the questions. Include justifications and citations from the learning resources or the findings from the hands-on exercises.
- Identify any vulnerabilities introduced by third-party libraries used in MedPeople’s web application. What are the specific risks associated with these libraries?
- Identify effective mitigation techniques to prevent both horizontal and vertical privilege escalation in MedPeople’s web application. How could these techniques be integrated into the application’s security framework to ensure robust defense against such exploitation?
- Given the sensitive nature of MedPeople’s web application dealing with patient data, assume a user role with restricted access. How would you test for IDOR vulnerabilities that might allow such a user to access or manipulate data beyond their privileges
- What specific parameters would you manipulate to test if access controls can be bypassed?
Tutorial for Program Analysis for Software Vulnerability Discovery
$30.00
